The breathless headlines about the “race for quantum supremacy” are, frankly, a distraction. While the theorists polish their algorithms and the venture capitalists dream of unicorn valuations, a far more immediate and unsettling reality is brewing: the impending quantum threat. This isn’t about hypothetical future machines; it’s about the very real possibility that sensitive data, encrypted today, could be harvested now and decrypted later by a quantum computer that might be closer than you think.
The Quantum Cryptography Race Against Time
Forget the sci-fi scenarios; we’re talking about cryptographic systems that underpin global finance, national security, and your everyday online life, all becoming vulnerable in a timeframe that makes “long-term” planning look like ancient history. The clock is ticking, and the silence from the traditional security sector is, frankly, deafening.
The Quantum Supremacy Race: H.O.T. Framework’s Measurable Frontier
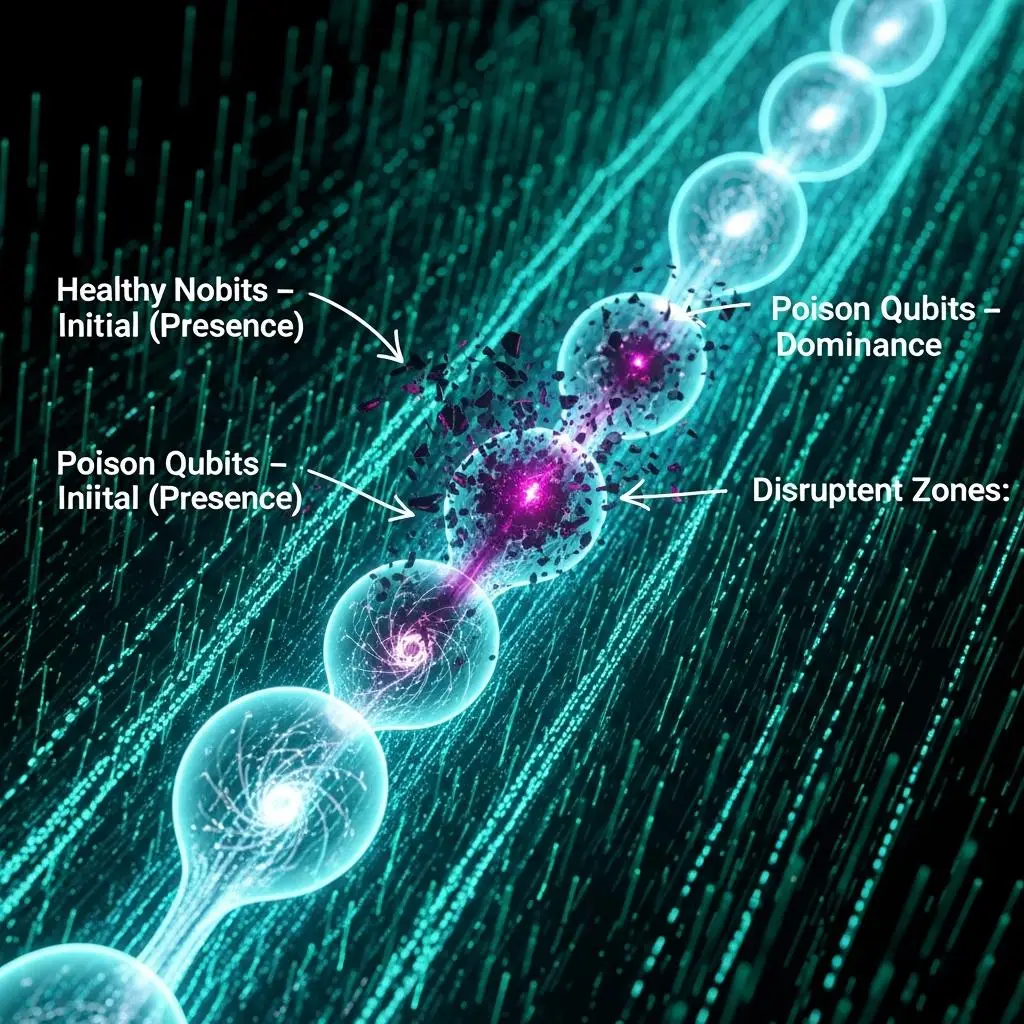
Here’s a supposition for you to test, a different way to frame the *real* benchmark for the quantum threat, beyond the abstract benchmarks. It’s about moving beyond the theoretical and into the measurable, using the **H.O.T. Framework**. We’ve identified a critical operational boundary we’re calling the “Dominance vs. Presence” collapse.
The Noise Race: Outpacing Quantum Supremacy
The real insight comes when you start quantifying the *ratio* of these poison qubits relative to your active computational space. The benchmark is about demonstrating that you can solve a real problem *despite* the hardware’s limitations, by understanding and actively managing the noise floor. The real threat isn’t the theoretical capability of a million-qubit machine; it’s the practical capability of a noisy machine that can break your crypto *today* if programmed smartly, by pushing past the perceived limits.
The Real Race: Quantifying the Quantum Threat
This isn’t about achieving a “quantum advantage” in a theoretical sense. We’re not asking you to chase “quantum supremacy.” We’re asking you to identify the “quantum threat.” Your benchmark isn’t how many gates you can run, but how many *useful* bits of information you can extract from a noisy computation, and at what poison qubit ratio you fail. Go ahead, measure it. The future of cryptography might depend on it.
For More Check Out