Alright, let’s talk about this “quantum supremacy experiment” hype. You see the headlines, right? “Quantum computers have finally surpassed classical ones!” Sounds like we should all be throwing our laptops in the bin, but if you’ve spent any time poking around the actual hardware, you know it’s not that simple.
Quantum Supremacy Experiment: A Classical Veto
The reality is, the moment a quantum system throws out an answer, it’s the classical computers – the ones we’ve been using forever – that get to decide if that answer is even remotely useful. It’s less about a decisive “win” and more about a perpetual debate between two very different kinds of computation, where the classical machine still holds the ultimate veto.
Quantum Supremacy Experiment: The Readout Reality
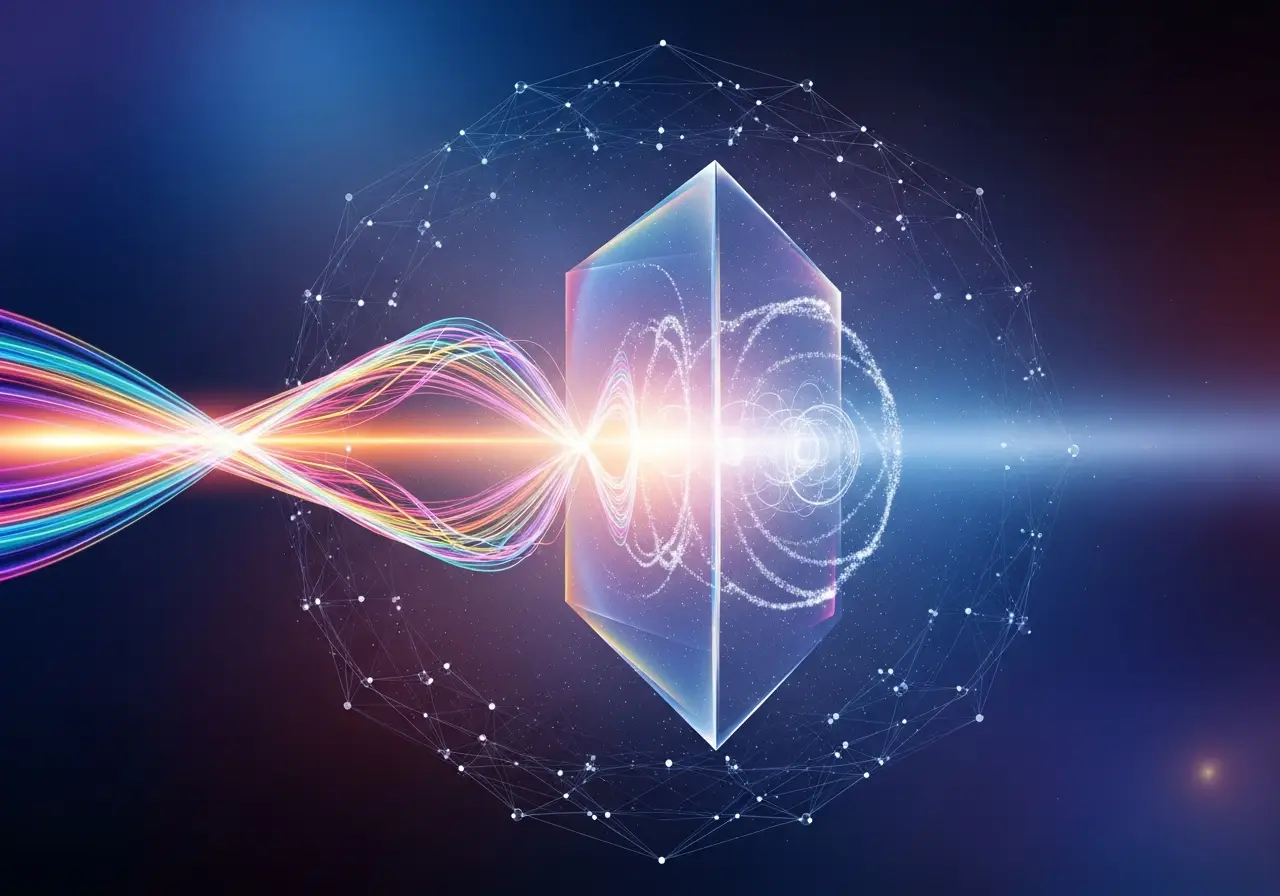
This “quantum supremacy experiment” narrative conveniently glosses over the core reality of our current quantum programming stack: the *real* bottleneck, the *actual* gatekeeper, isn’t the number of gates or qubits, but the latency and integrity of the readout. We’re not building idealized circuits and *hoping* for the best. We’re engineering for the concrete, the noisy, the *real* hardware fingerprints we encounter daily.
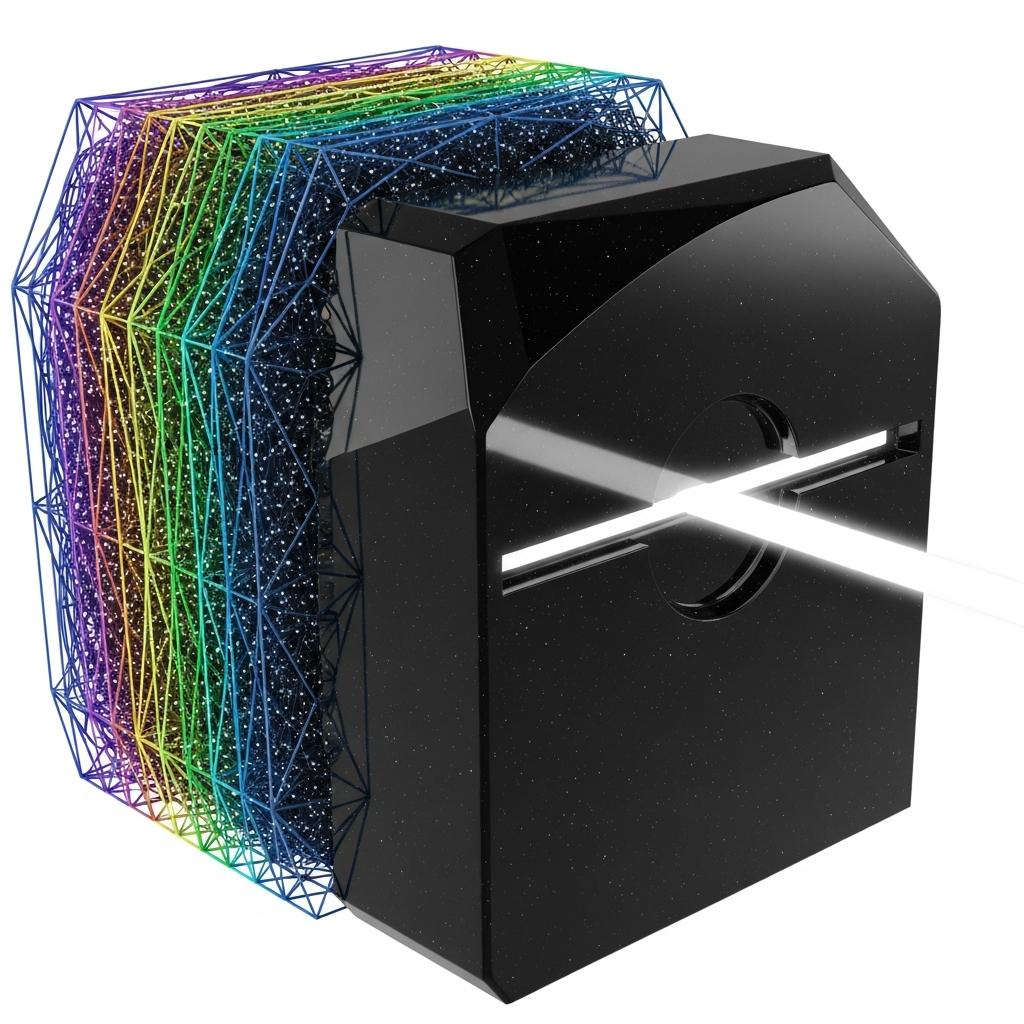
Quantum Supremacy Experiment: The V5 Measurement Discipline
Consider the V5 orphan measurement exclusion. We’re implementing Shor-style period finding for Elliptic Curve Discrete Logarithm Problems (ECDLP) on real hardware. Each elliptic curve double or add operation is designed to be algorithmically sound, but physically realized in a way that cancels a significant portion of coherent errors. The whole shebang is then wrapped in that V5 measurement discipline. We reject the shots and qubits that signal anomalous behavior, and reconstruct the hidden period from the surviving, higher-fidelity data.
Quantum Supremacy Experiment: Classical Disposition
So, when you see those “quantum supremacy experiment” headlines, remember this: the quantum computer proposes, but the classical machine *disposes*. It’s the classical system’s relentless scrutiny, its ability to analyze raw measurement telemetry, that truly determines utility. The real benchmark isn’t a theoretical “supremacy,” but the verifiable recovery of non-trivial cryptanalytic targets on existing, noisy hardware. This isn’t science fiction; this is hardware-aware quantum programming. And it’s what we’re doing.
For More Check Out